DigiCert Breach Explained: How the Certificate Authority Set the Gold Standard for Incident Response
AI-generated, human-reviewed.
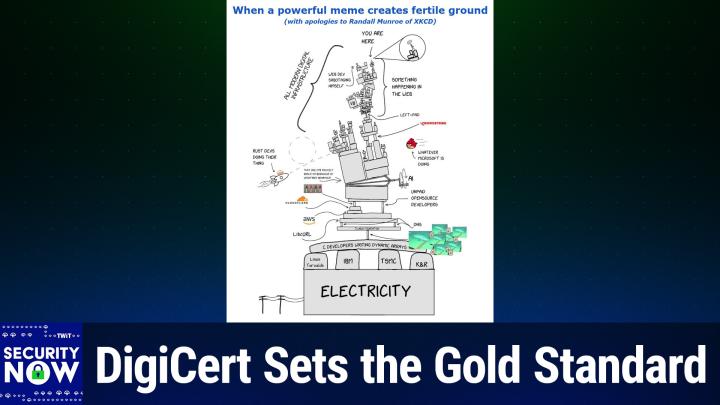
When a certificate authority is breached, the impact can ripple across the internet. On Security Now, Steve Gibson analyzed DigiCert’s recent security incident, revealing how their thorough, transparent response not only limited potential fallout but also serves as a playbook for incident management.
Below, we’ll explain what happened, why Microsoft’s reaction caused additional trouble, and what you should be looking for from companies handling your digital trust.
What Happened in the DigiCert Breach?
In early April 2026, DigiCert—one of the largest and most trusted certificate authorities (CAs) worldwide—was targeted by a malware campaign. Attackers compromised internal support endpoints by tricking staff into opening infected files via a customer support portal. This allowed the attackers to acquire unique certificate initialization codes for extended validation (EV) code signing certificates before they were delivered to legitimate customers.
Armed with these codes, the attackers were able to obtain 27 fraudulent code signing certificates, which were then used to sign and distribute malware, including the "Zong Stealer" campaign linked to Chinese crime groups.
Significantly, DigiCert’s root certificates were never compromised. The breach was limited to a finite set of certificates, thanks in part to both internal monitoring and help from security researchers who quickly reported the malicious certificates.
How DigiCert Handled the Incident – A Model for Transparency
According to Steve Gibson on Security Now, DigiCert’s approach to disclosure and remediation stood out for its clarity, detail, and responsibility. Within 24 hours of discovery, all affected certificates were revoked, with revocation set to the original issue date to prevent further misuse.
DigiCert’s incident report thoroughly documented every phase: how the breach occurred, contributing technical and procedural weaknesses (such as incomplete endpoint protection and insufficient privilege controls), and the precise remediation steps taken. Actions included:
- Blocking affected endpoints.
- Masking access to sensitive data in the support portal.
- Improving malware scanning for all support channel file uploads.
- Reviewing privilege access management and threat models organization-wide.
This “no corners cut” approach gave the community confidence in their processes and enabled rapid response from other ecosystem stakeholders.
Microsoft Defender: A Case Study in What Not to Do
While DigiCert’s response was widely praised, Microsoft Defender’s handling of the aftermath created a new set of problems. Instead of simply blocking the compromised certificates, Microsoft Defender updates began detecting and deleting DigiCert’s root certificates from Windows Trust Stores on countless devices.
This overreaction caused widespread disruption: legitimate software signed by DigiCert was suddenly marked untrusted, leading to false alarms and some users unnecessarily reinstalling Windows. After significant industry chatter and rapid feedback, Microsoft pushed a fix to restore certificates. Still, the episode highlighted the dangers of automated responses that lack situational awareness or proper validation, especially with root infrastructure.
Why Certificate Authority Breaches Matter
Certificate authorities play a critical role: they underpin the trust model that enables secure web browsing, software downloads, and encrypted communications. If this trust anchor is compromised or mishandled, it can have catastrophic security and usability implications.
DigiCert’s breach underscores how attackers are increasingly targeting trusted infrastructure to facilitate attacks, using legitimate certificates to bypass protections and infect end-users. However, it also shows that rigorous monitoring, clear access controls, and a culture of transparency dramatically limit the damage and maintain stakeholder trust.
What You Need to Know
- DigiCert was breached through a support portal malware attack, leading to misuse of 27 code signing certificates.
- All affected certificates were revoked within 24 hours of discovery.
- DigiCert’s communication and internal review set a strong example of transparent, actionable incident management.
- Microsoft Defender’s overzealous response inadvertently caused additional problems by removing legitimate root certificates.
- No end-user action is needed if running current Microsoft security updates, as they have restored affected certificates and resolved false positives.
- The episode highlights the critical value of layered security, third-party reporting, and continuous privilege/access review within organizations.
- Attacks on trust infrastructure (like CAs) are becoming more attractive to cybercriminals. Vet vendors for clear response plans and willingness to take responsibility.
The Bottom Line
When trust anchors of the digital world are targeted, the response of vendors shapes the impact. DigiCert’s fast, open, and technically sound approach not only protected users but set a high bar for transparency in the cybersecurity industry. Meanwhile, Microsoft’s hasty automation underlines the need for careful, informed handling of root trust issues.
For IT teams, business leaders, and cybersecurity professionals, this event is a reminder: expect attackers to try creative paths to your critical infrastructure—and prepare your monitoring, incident response, and communications accordingly.
Subscribe for more insights and thorough security analysis:
https://twit.tv/shows/security-now/episodes/1078